Modern Workplace
Device and application management
- Flexibility & mobility
- Mobile Device Management (MDM)
- Cloud services
- Greater security
Zero Trust, VPNs and endpoint protection
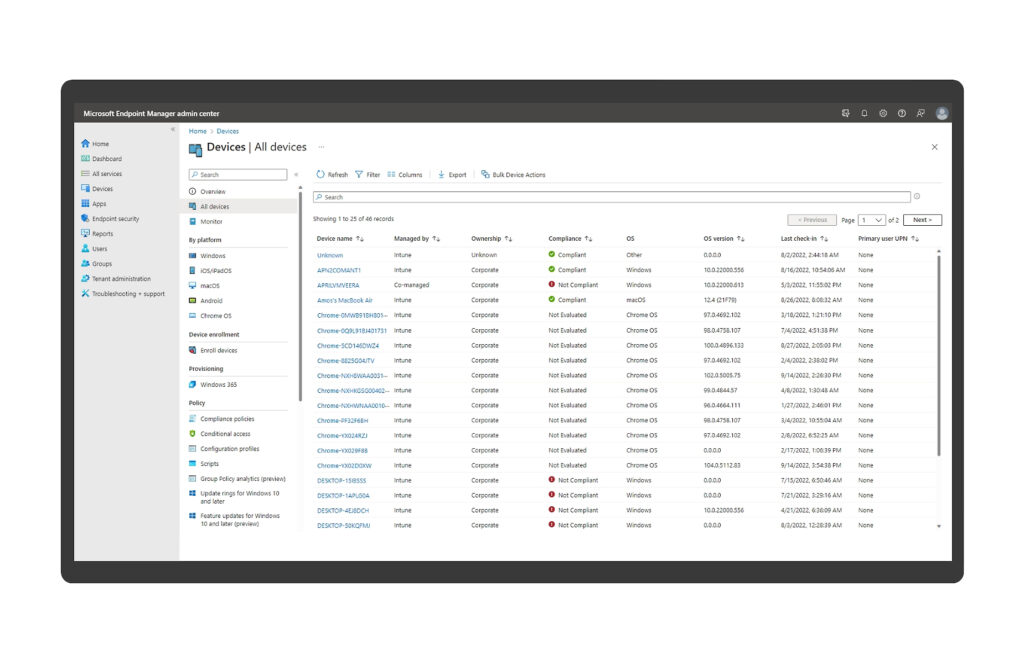
Microsoft Intune
- Comprehensive update management Automation of patch cycles while retaining control over the deployment phases.
- Secure configuration basics, according to the CIS (Center for Internet Security) framework to enforce hardened security postures on all devices.
- Real-time monitoring of device compliance status to ensure that only trusted, compliant devices access corporate resources.
- Unified management of mobile applications with policy-based controls for deployment, access and data protection across multiple platforms.
Global Secure Access
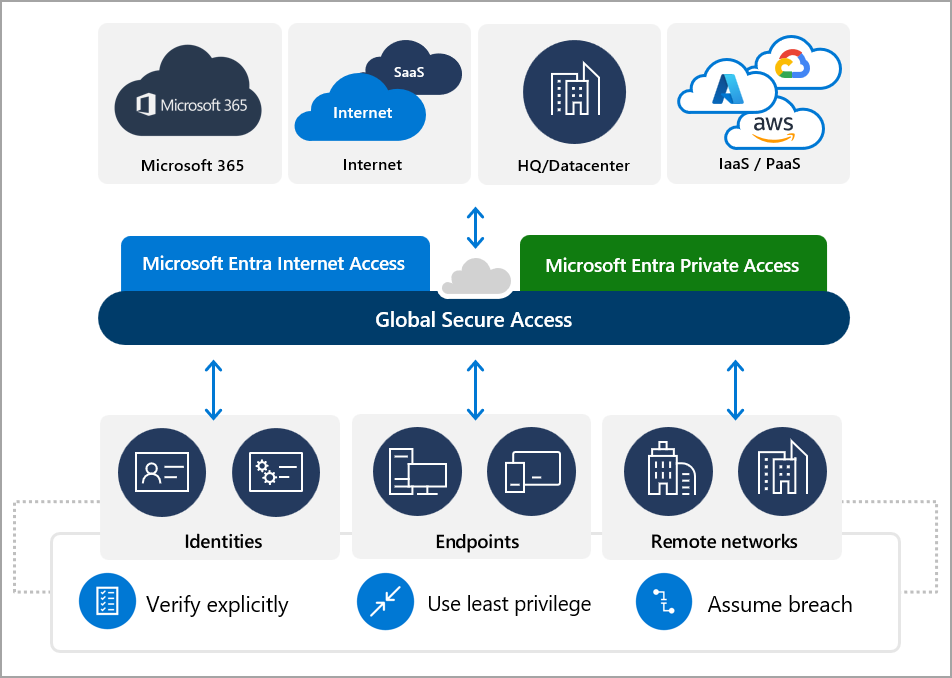
- Uniform security
- Secure from anywhere
- Trust through control
Password Manager
Most projects do not need a disruptive full reset. We usually start with a scoped rollout: identify the most important device groups, define security baselines, connect identity and compliance policies, and then enroll devices in phases. That reduces risk, avoids overwhelming users, and lets you see value early instead of waiting for a long all-at-once migration.
No. The goal is the opposite: fewer manual setups, faster onboarding, and more predictable access to apps and data. With the right policies in place, users receive secure configurations automatically, new devices can be prepared with minimal hands-on effort, and access decisions happen in the background based on identity and device trust.
Yes, but it is not recommended. We design policies differently for corporate-owned and personal devices so that company data is protected without unnecessarily intruding into private use. That is especially important for organizations with mixed work models, external partners, or mobile-heavy teams.
We’ll support ongoing device enrollment, policy maintenance, application rollout, update management, compliance monitoring, and adjustments when new requirements arise. That means you are not left with a one-time implementation that your internal team must suddenly operate alone.
A modern workplace reduces blind spots. Geräte werden registriert, Konfigurationsstandards zentral durchgesetzt, Updates lassen sich einheitlicher steuern und der Zugriff auf Ressourcen kann an die Benutzeridentität und die Gerätekonformität gekoppelt werden. This lowers the chance that unmanaged, outdated, or risky devices gain access to company systems.